Our Company
Our Community

Executive team

Partners & Clients
News
Events
Digital Transformation
Cybersecurity

Security Advisory Services
CISO Services, Security Program Management, Digital Forensics & Incident Response (DFIR)

Assessment Services
PCI Compliance and Assessment, Third-Party Risk Assurance, Risk & Privacy Readiness Assessment and Remediation, Compliance and Assessments: ISO, NIST, SOC, GDPR
Innovation Lab
CURRENT OPENINGS

OUR CULTURE
OUR BENEFITS
CULTURE CREDO
Blog
Customer Experience
Agile Transformation
B2B eCommerce
FINANCIAL SERVICES

Contact Us

Locations
Our Company
Our Community

Executive team

Partners & Clients
News
Events
Digital Transformation
Cybersecurity
Innovation Lab
CURRENT OPENINGS

OUR CULTURE
OUR BENEFITS
CULTURE CREDO

Blog
Customer Experience
Agile Transformation
B2B eCommerce
FINANCIAL SERVICES

Contact

Locations
WHAT IS SECURITY PROGRAM MANAGMENT?

"Good security is more than a combination of technologies and services; Online’s experts can help you architect a scalable, risk-appropriate, and effective program."
Steve Levinson, Vice-President, RSP, Online Business Systems
SECURITY PROGRAM MANAGEMENT WITH ONLINE
Our seasoned practitioners work with clients to set the foundation for a right-sized security program by establishing the mission, goals, technologies, and processes to maintain and improve the program. All this is done to ensure that the security program is aligned with the organization’s strategic business objectives in an ever-changing risk landscape.
OUR APROACH
When building out a security program with our clients, Online takes a three-step approach.
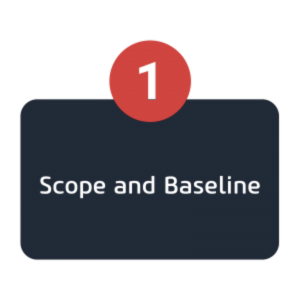
In Step 1, we identify the key people, technologies, and processes to protect your critical assets. Online experts then perform an assessment that may look at asset and data inventories, dataflows, architecture diagrams, etc., while considering legal, regulatory and contractual requirements.
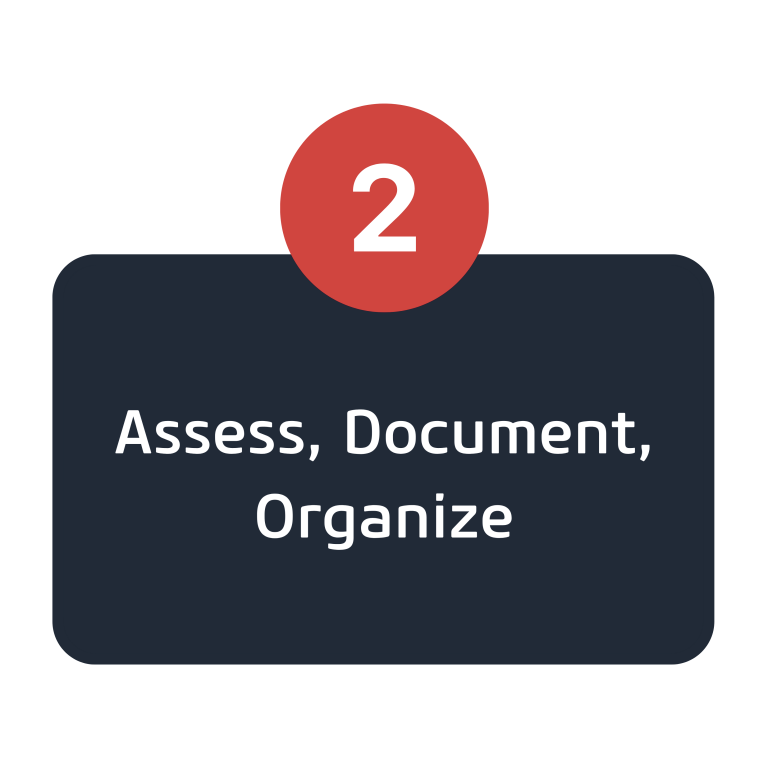
A comprehensive risk assessment occurs in Step 2, resulting in a remediation roadmap and/or a formal risk register. To build or improve the security program, Online will work with our clients to prioritize the remediation activities, considering risk, perceived level of effort to remediate, costs, resource availability and timelines.
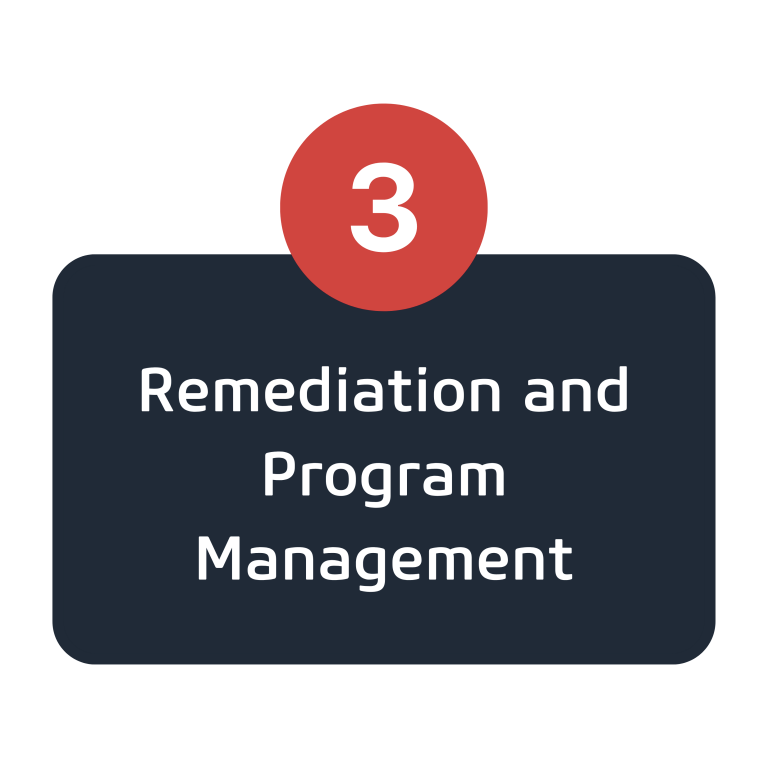
Optionally, Online may provide remediation activities such as security policy development, incident response planning, vulnerability management, security awareness training, third-party risk management and security event monitoring guidance.
BLOG: TOP 5 SIGNS YOU NEED A VIRTUAL CISO
Medical records created and maintained by health care organizations must remain confidential, accurate, and accessible. However, many organizations don't have the internal capabilities to comply with these regulations and cannot afford to hire experts in these fields. In such a case, a virtual Chief Information Security Officer, or vCISO, can be beneficial.