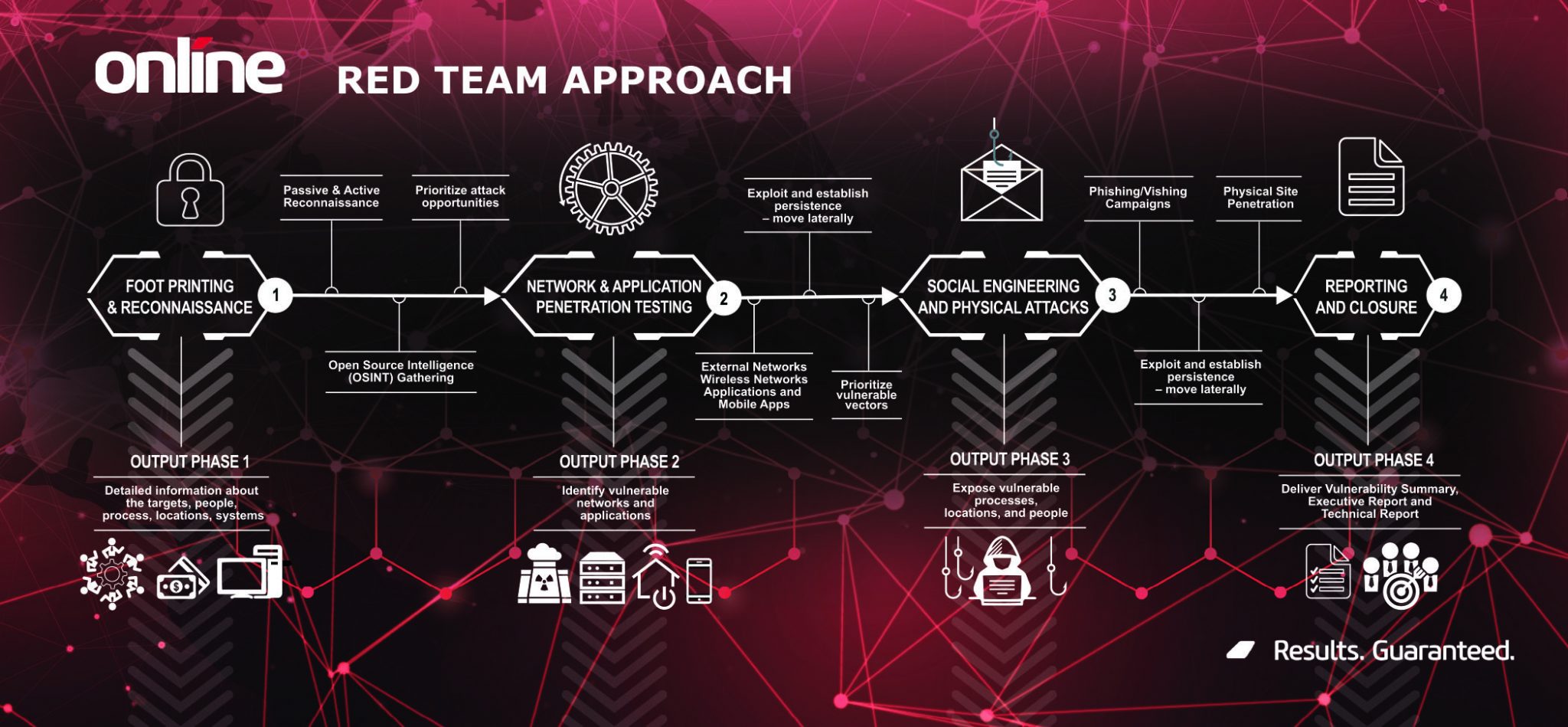
Penetration Testing & Red Teaming
Research shows that US organizations are reporting an increase of over 41% in compromised files in a one year period.
In one month alone, the average payment demand was $190,946 with several organizations facing ransom demands in the millions of dollars.
In one month alone, the average payment demand was $190,946 with several organizations facing ransom demands in the millions of dollars.