Our Company
Our Community

Executive team

Partners & Clients
News
Events
Digital Transformation
Cybersecurity

Security Advisory Services
CISO Services, Security Program Management, Digital Forensics & Incident Response (DFIR)

Assessment Services
PCI Compliance and Assessment, Third-Party Risk Assurance, Risk & Privacy Readiness Assessment and Remediation, Compliance and Assessments: ISO, NIST, SOC, GDPR
Innovation Lab
CURRENT OPENINGS

OUR CULTURE
OUR BENEFITS
CULTURE CREDO
Blog
Customer Experience
Agile Transformation
B2B eCommerce
FINANCIAL SERVICES

Contact Us

Locations
Our Company
Our Community

Executive team

Partners & Clients
News
Events
Digital Transformation
Cybersecurity
Innovation Lab
CURRENT OPENINGS

OUR CULTURE
OUR BENEFITS
CULTURE CREDO

Blog
Customer Experience
Agile Transformation
B2B eCommerce
FINANCIAL SERVICES

Contact

Locations

WHAT IS SECURE CODE REVIEW?
In addition to identifying vulnerabilities, a secure code review seeks to identify insecure design patterns and weak coding practices. Once identified, developers can leverage this knowledge to create more secure code in the future.
KEY BENEFITS OF A SECURE CODE REVIEW
EARLY PROBLEM IDENTIFICATION
Known in the industry as “Shift Left Testing,” Security flaws and weaknesses can be identified and addressed before the application is pushed to production by performing secure code reviews early in the development process. This can be very valuable in the design and architecture stage of an application’s development cycle.
COST & TIME SAVINGS
Detecting and resolving vulnerabilities earlier can save companies time, money, and resources. This translates into reduced costs and time to identify, fix, and debug vulnerabilities.
ENCOURAGES HEALTHY CODING PRACTICES
Performing Secure Code Analysis verifies the integrity of the application’s code and ultimately improves the overall coding standards of your organization. In addition, it encourages developers to create robust and stable applications, resulting in fewer errors like memory leaks, insecure logic and anti-patterns.
ONLINE'S SECURE CODE ANALYSIS & REVIEW SERVICES
Our Secure Code Reviews follow a detailed process that utilizes dynamic and static tools, ultimately compiling a report that details our findings.
THE SECURE CODE REVIEW PROCESS
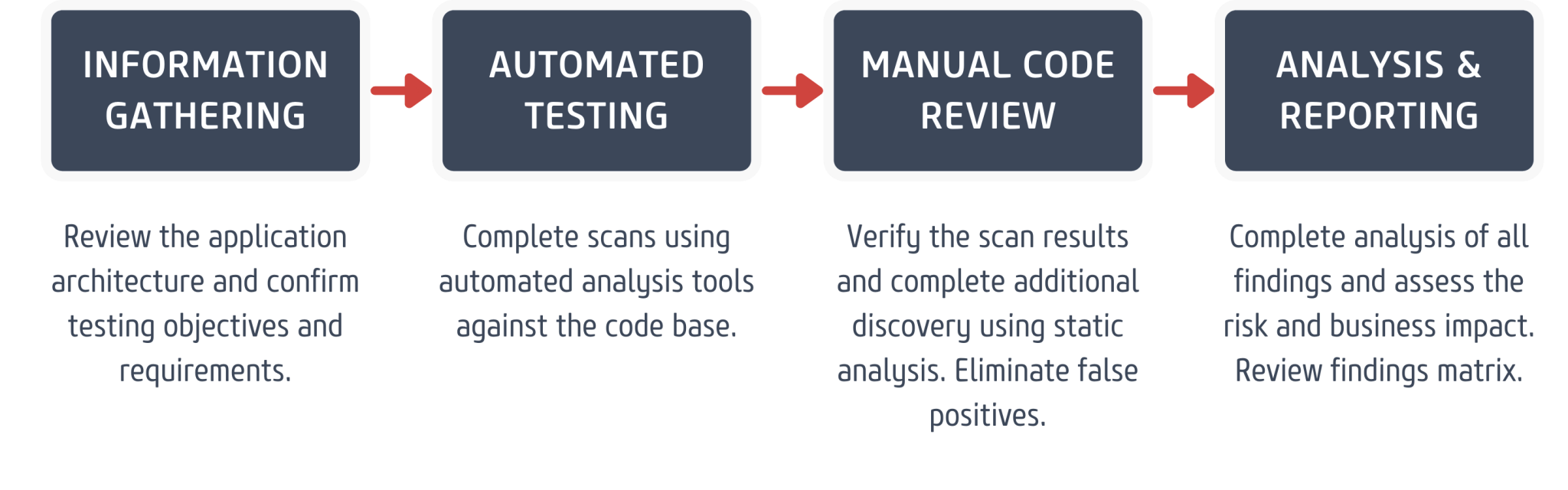

We help identify potential issues with architecture, integration, and user requirements early in the lifecycle so your software is built and implemented securely from the start.
Steve Levinson, Vice-President, RSP, Online Business Systems
BLOG: INSECURE CODING CAN LEAD TO A ZOMBIE APOCALYPSE
A zombie alert in Lake Worth, Florida, has made headlines worldwide. Laughter aside, this hack is another helpful reminder to ensure that our applications are reasonably secure. Coding errors could have had much more severe and harmful consequences.